TLS 1.0 is end of life on June 30, 2018. To disable TLS 1.0 on nginx webserver installations, edit the “ssl_protocols” directive in your nginx.conf, where the TLS server directives are listed and remove TLSv1. By restarting the nginx, after updating the ssl_protocols directive TLS 1.0 will be disabled.
Here are steps how to disable TLS 1.0 on a nginx server.
Table of Contents
Backup nginx configuration
Copy the nginx.conf before the TLS change. This is recommended before you do any change to critical configuration files.
cp /etc/nginx/nginx.conf /etc/nginx/nginx.conf-backup-pre-tlschangeUpdate the Configuration file nginx.conf
The default configuration looks like this , where you can check the TLS protocols on ssl_protocols keyword highlighted as below:
server { listen 443 ssl http2 default_server; listen [::]:443 ssl http2 default_server; server_name _; root /usr/share/nginx/html;ssl_certificate "/etc/ssl/certs/cloudibee-lab-nginx.crt"; ssl_certificate_key "/etc/pki/nginx/cloudibee-lab-nginx.key"; ssl_session_cache shared:SSL:1m; ssl_session_timeout 10m; ssl_ciphers HIGH:!aNULL:!MD5; ssl_protocols TLSv1 TLSv1.1 TLSv1.2; ssl_prefer_server_ciphers on; ... }You will see a directive for “ssl_protocols”, which has TLS 1.0, TLS 1.1 and TLS 1.2 version-enabled. In some installations, you will not see the ssl_protocol directive. In that case, just add “ssl_protocols TLSv1.1 TLSv1.2” to the configuration file.
ssl_protocols TLSv1 TLSv1.1 TLSv1.2;Edit it and change to:
ssl_protocols TLSv1.1 TLSv1.2;This will specifically allow only TLS 1.1 and TLS 1.2.
Restart nginx after configuration change
After you update the configuration file, restart the nginx server.
service nginx restartor
systemctl restart nginx.serviceYou are done.
You can also confirm this with nmap or ssl-scan utility to make sure TLS 1.0 is disabled. [ https://cloudibee.com/ssl-cert-tools/ ]
Verifying configuration change using nmap command
Before disabling :
You can see that the host serves TLS 1.0, TLS 1.1 and TLS 1.2.
[[email protected] ~]# nmap --script ssl-enum-ciphers -p 443 192.168.200.101Starting Nmap 7.40 ( https://nmap.org ) at 2018-01-26 15:19 PST Nmap scan report for 192.168.200.101 Host is up (0.00044s latency). PORT STATE SERVICE 443/tcp open https | ssl-enum-ciphers: | TLSv1.0: | ciphers: | TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA (secp256r1) - A | TLS_RSA_WITH_AES_256_CBC_SHA (rsa 2048) - A... | TLS_RSA_WITH_CAMELLIA_128_CBC_SHA (rsa 2048) - A | compressors: | NULL | cipher preference: server | TLSv1.1: | ciphers: | TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA (secp256r1) - A | TLS_RSA_WITH_AES_256_CBC_SHA (rsa 2048) - A... | TLS_RSA_WITH_CAMELLIA_128_CBC_SHA (rsa 2048) - A | compressors: | NULL | cipher preference: server | TLSv1.2: | ciphers: | TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384 (secp256r1) - A | TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384 (secp256r1) - A... | TLS_RSA_WITH_CAMELLIA_128_CBC_SHA (rsa 2048) - A | compressors: | NULL | cipher preference: server |_ least strength: A Nmap done: 1 IP address (1 host up) scanned in 0.42 seconds [[email protected] ~]#After disabling :
You can see that TLS 1.0 cipher is no longer served by the host.
[[email protected] ~]# nmap --script ssl-enum-ciphers -p 443 192.168.200.101Starting Nmap 7.40 ( https://nmap.org ) at 2018-01-26 15:19 PST Nmap scan report for 192.168.200.101 Host is up (0.00034s latency). PORT STATE SERVICE 443/tcp open https | ssl-enum-ciphers: | TLSv1.1: | ciphers: | TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA (secp256r1) - A... | TLS_RSA_WITH_CAMELLIA_128_CBC_SHA (rsa 2048) - A | compressors: | NULL | cipher preference: server | TLSv1.2: | ciphers: | TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384 (secp256r1) - A... | TLS_RSA_WITH_CAMELLIA_128_CBC_SHA (rsa 2048) - A | compressors: | NULL | cipher preference: server |_ least strength: ANmap done: 1 IP address (1 host up) scanned in 0.41 seconds [[email protected] ~]#Mozilla SSL Config Generator
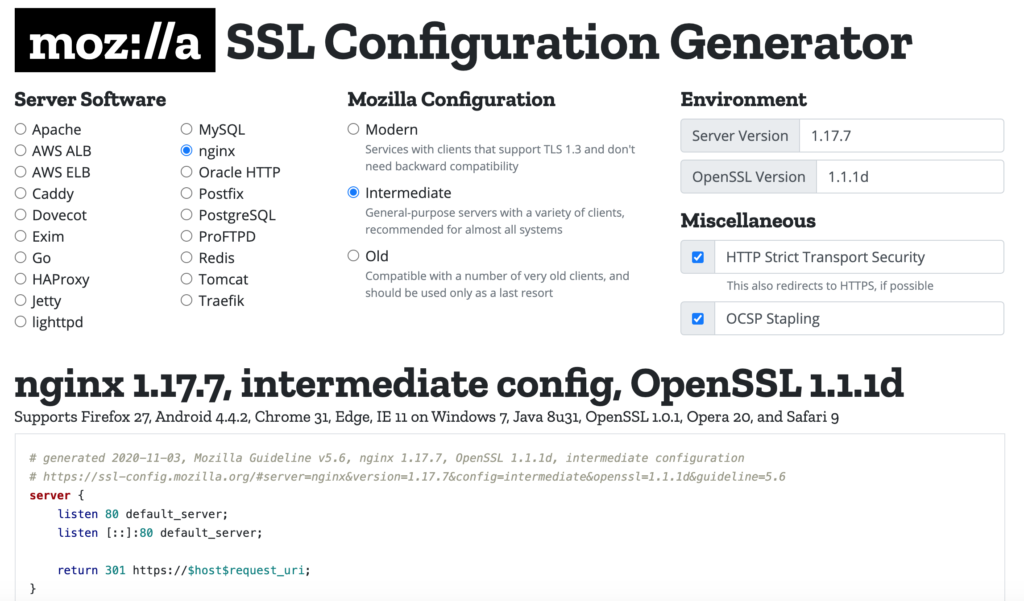
If you are looking for a SSL configuration generator for your apache, you can refer to https://ssl-config.mozilla.org/. This awesome tool from Mozilla provides you options to generate SSL configurations with various levels of input and how strict you want your SSL configuration should be.
Other good reference for generating configurations with strict security guidelines is https://cipherli.st/
Refer to https://cloudibee.com/disabling-tls-apache/ for disabling older TLS in Apache web server.
